Over the years, the Nickel Group has seen the need to standardize, standardize and facilitate collaboration between employees and IT systems. This approach allowed TCO (total cost of ownership) to be maintained despite the simultaneous increase in functionality and data processing security in subsequent IT implementations.
Data security has always been one of the critical points for protecting an enterprise’s IT systems. This notion has taken on particular importance in recent years, in which statistics show increased activity by hacking groups in creating malware.
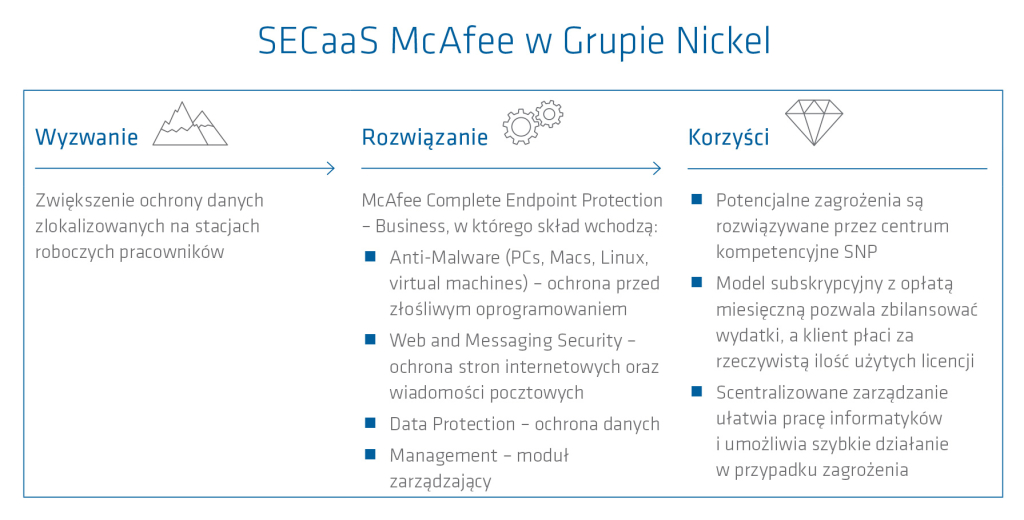
An audit conducted at the client’s site indicated the need for increased protection of data located on employee workstations. Antivirus protection is no longer sufficient protection, so the audit identified further areas where security improvements are indicated.
All of the customer’s needs were taken into account when selecting the product provided by SNP Poland (currently All for One Poland) in the SaaS (Security-as-a-Service) model.
Situation before implementation
Historically, the client had various antivirus protection products in Nickel Group companies. These products lacked a central management console to monitor threats in real time. One of the first recommendations after the start of the cooperation was the need to standardize the antivirus protection solution and provide a central management console. Such a solution provides the opportunity to reduce the total cost of workstation security management, license monitoring and threat reporting. The administrator is then able to know the scale of threats and react in real time to protect data. The results of the external audit also indicated the need to extend user security to protect data located on their workstations.
Data loss
A particular threat, underestimated in organizations, is the physical loss of a data carrier that most often contains vital information for the business.
Imagine a situation in which the laptop of a CEO, director or project manager is stolen. And it’s not just the loss of data itself, which the user should always recover by using a reliable, proven backup tool. A more significant problem could be access to confidential data by unauthorized third parties who come into possession of a stolen device (economic espionage).
Let’s use actual events as examples:
- A flash drive with secret Swedish Secret Service data left in a library in Stockholm (2008),
- The Financial Services Authority (FSA) has fined Nationwide Building Society (Nationwide) $980,000 for inadequate data leak protection systems (employee computer theft – 2006).
As studies have shown, the estimated statistical cost of a single piece of information lost (Personally Identifiable Information) is $194 (Ponemon Institute, 2011).
The above takes on new importance in the context of the new European requirements for personal data (GDPR / RODO) coming into force in May 2018.
For the example situation described above, the use of a suitably complex disk/partition encryption algorithm can provide protection. Such technology is provided by one of the modules available in McAfee’s SECaaS product: the Drive Encryption module described later in this article.
A good solution
The McAfee product includes various modules and functionalities that can be configured within a specific package.
The majority package deployed at the Nickel Group called McAfee Complete Endpoint Protection – Business includes components such as:
- Anti-Malware (PCs, Macs, Linux, virtual machines) – protection against malware.
- Web and Messaging Security – protection of web pages and mail messages.
- Data Protection
- Management – management module.
The whole thing is efficiently managed by the McAfee agent, which we can observe on the user’s workstation in the system tray in the form of a contemporary-looking icon: ![]()
When you right-click on the McAfee agent icon, choices are available:
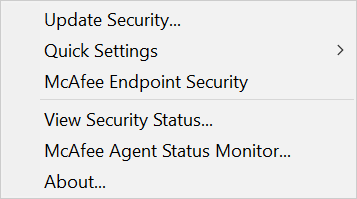
Fig. 1
Anti-Malware (PCs, Macs, Linux, virtual machines) – protection against malware.
The core protection modules include the powerful McAfee Endpoint Security 10 (ENS) antivirus engine.
It is worth mentioning at this point that the previous engine version McAfee VirusScan Enterprise 8.8 (VSE 8.8.) is now being replaced globally by the optimized ENS 10. SNP Poland (currently All for One Poland) has experience in migrating customers from the previous antivirus engine version to the new one. The migration process to the new ENS 10.5 antivirus engine is performed in the background and is “transparent" to the end user.
Selecting the McAfee Endpoint Security item shown in Figure 1. allows access to clear information of the antivirus engine (Fig. 2.)

Fig. 2
Web and Messaging Security – protection of web pages and mail messages.
This component includes:
- Site security assessment (Fig. 3)
- Ability to block/warn about dangerous or unwanted websites visited – the engine uses a global list of suspicious sites. If you try to enter a suspicious site, you will be prompted (Fig. 4)
- in this case, after clicking OK, you will be able to enter the site, but remember to use this option consciously, because the low reputation of the site may have its grounds
- Enhanced anti-spam protection at the Outlook mail client level (Fig. 5)
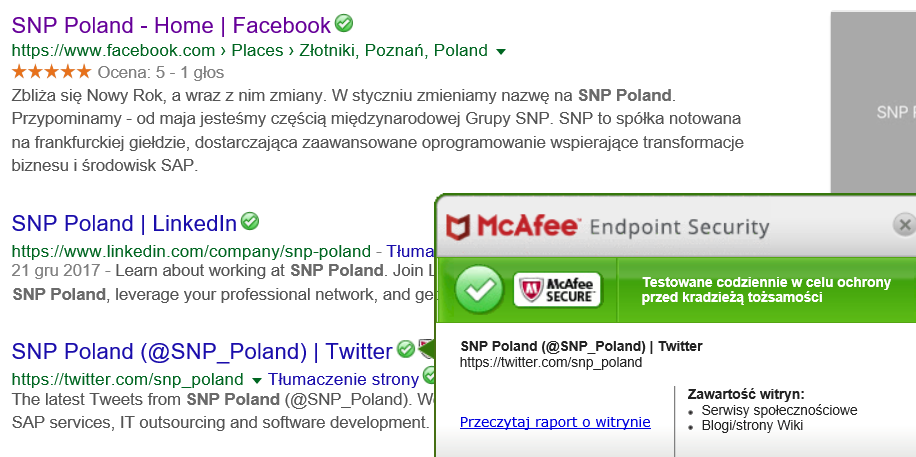
Fig. 3
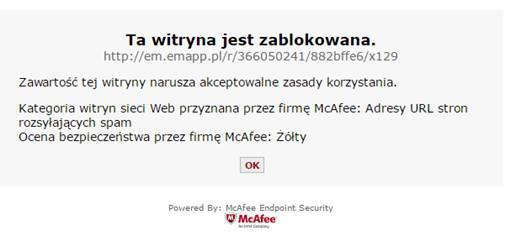
Fig. 4
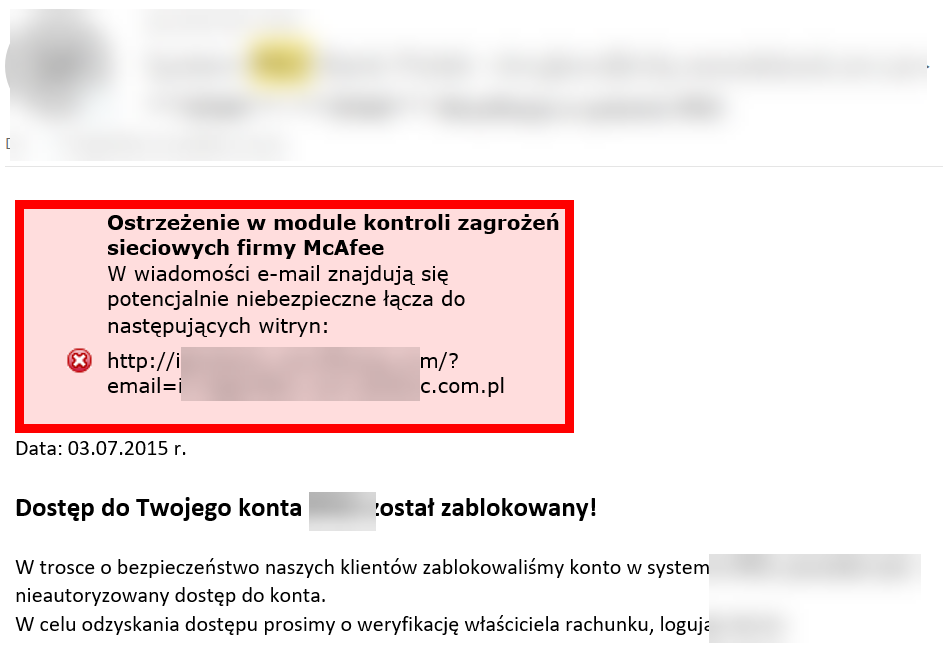
Fig. 5
Data Protection
One of the most important modules is the Data Protection component, which is responsible for, among other things, encrypting workstation drives accessible by selecting Quick Settings (see Figure 1).
Then we can view the current status of disk protection (Fig. 6).
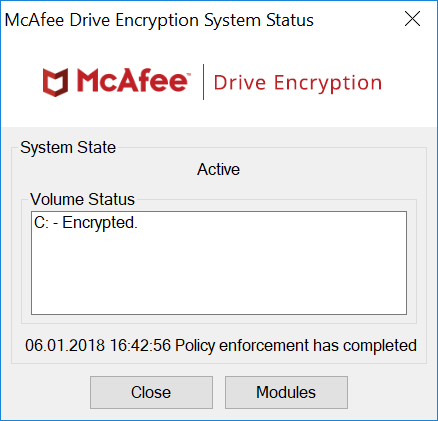
Fig. 6
Disk encryption is done “on the fly", and the user can work on his station at all times. Pay special attention to the fact that encryption should be preceded by backing up data. Let’s remember that the encryption process should protect our data from an attempt, for example, to physically remove the disk from the computer and read it in another machine. Therefore, regular backups are essential to preserve the integrity of the data throughout its “life".
Management – product management
McAfee Endpoint Security policies can be managed from the ePolicy Orchestrator (ePO) central management console. This is especially important when you need to efficiently update McAfee settings, configurations, policies and components on workstations.
The user is able to monitor automatic communication (and mix manually if necessary) with the ePO console by selecting the McAfee Agent Status Monitor item shown in Fig. 1. When this function is selected, information is available as shown in Fig. 7.
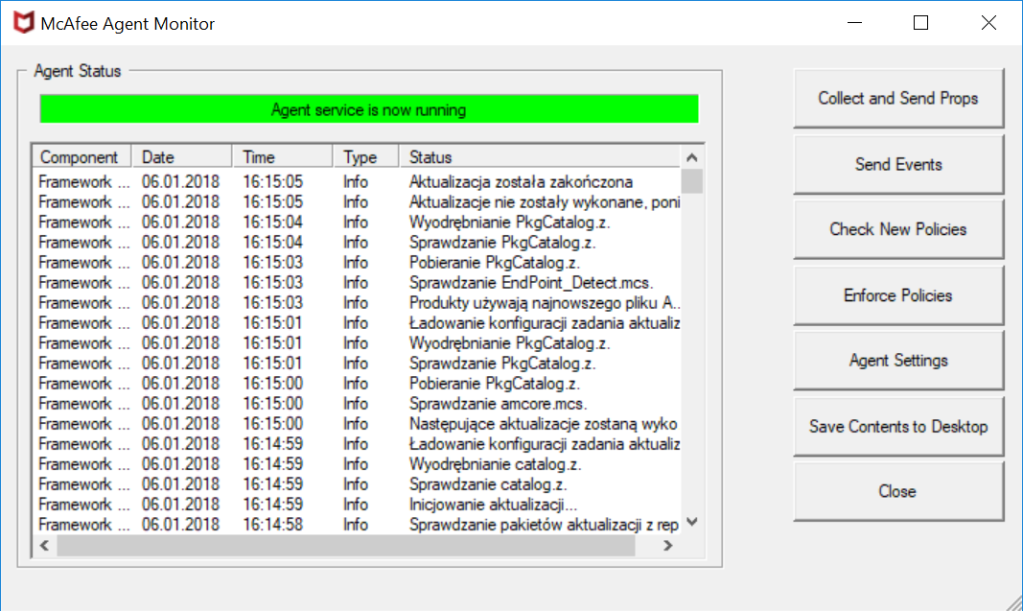
Fig. 7
What has changed?
-
Security
The implementation of McAfee-based SECaaS has reduced the complexity of the end-to-end security environment, provided better protection for users and their data, and enabled faster response when advanced threats are detected.
-
Direct product support
The first line of support for the SECaaS service is provided by SNP Poland (currently All for One Poland) consultants, who are familiar with the customer’s experience with the implementation and daily use of the product. Most potential requests can be resolved by the competence center located at SNP Poland to provide direct, efficient and high-quality support to customers.
-
Licensing
The Nickel Group does not have to search for solutions on its own, monitor licensing issues, and keep an eye on the expiration date of licenses or product support.
-
Fee flexibility (subscription)
Until now, the customer was forced to buy/renew annual antivirus packages. In addition to the large annual one-time cost, there was the issue of renewing a specific (originally purchased) license. Even when part of the license was not used at any given time.
The McAfee SECaaS product provided by SNP Poland ensures the transition to a fully subscription model. The monthly billing proposed to the Nickel Group helped balance expenses on an annual basis. Most importantly, the product itself is delivered in a pay-as-you-use model, meaning the customer pays monthly for the actual number of licenses used per user.
Safe work without danger
McAfee-based SECaaS is a comprehensive solution that uses common global threat detection. It allows you to defend against advanced threats, and disk encryption to protect data physically secures media from unauthorized access. Phishing and multi-stage attacks are also blocked through email verification. Finally, centralized management simplifies the day-to-day work of IT staff and enables quick action in the event of a threat. The holistic approach on the part of SNP Poland (now All for One Poland) consultants has made it possible to increase the security of data located on Nickel Group employees’ workstations.

Maciej Sobkowiak, legal and administrative director, Nickel Development Sp. z o.o.
SNP Poland consultants supported the Nickel Group at every stage of the implementation of the end-user IT data protection solution. It was particularly important for us to precede the implementation with confirmation of backup. SNP Poland (now All for One Poland) supported us in this area as well.
End-user station protection in the SECaaS model, although marginally more expensive than traditional annual licensing, allows us to optimize our IT budget and have complete flexibility in terms of staff and hardware, as well as the freedom to replace the solution with another one in the future. This is because with monthly payments, we pay for the actual number of users covered in a given month without any further obligations and long amortization periods for one-time expenses.
Maciej Sobkowiak, legal and administrative director, Nickel Development Sp. z o.o.
The Nickel Group is made up of the construction company PTB Nickel, the development company Nickel Development and the technology park YouNick. All of the Nickel Group’s companies operate on the principle of co-creating space with its users. At the construction company PTB Nickel and the development company Nickel Development, the area of cooperation is a comfortable place to live. In the YouNick Technology Park, on the other hand, a place to work and do business.

